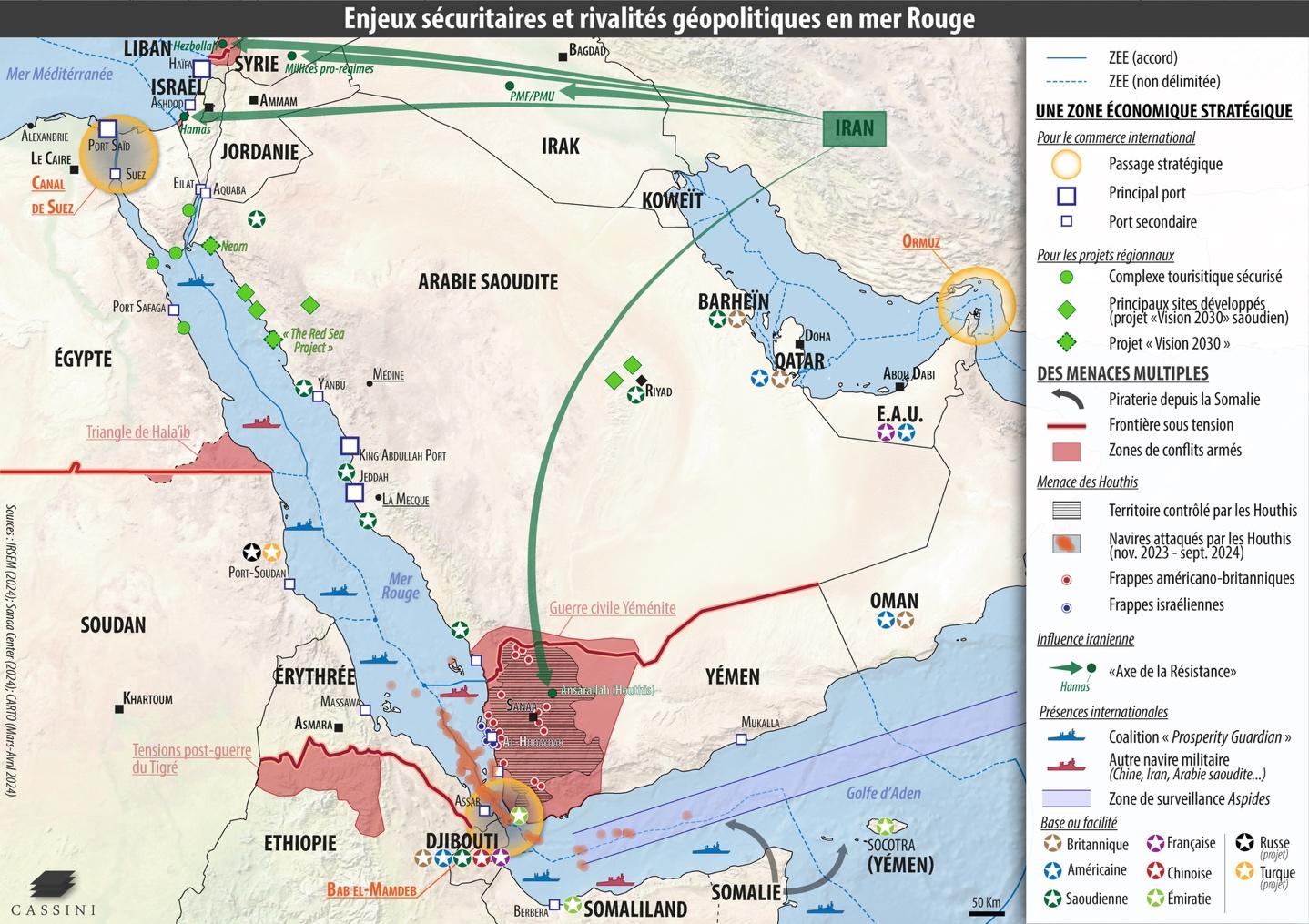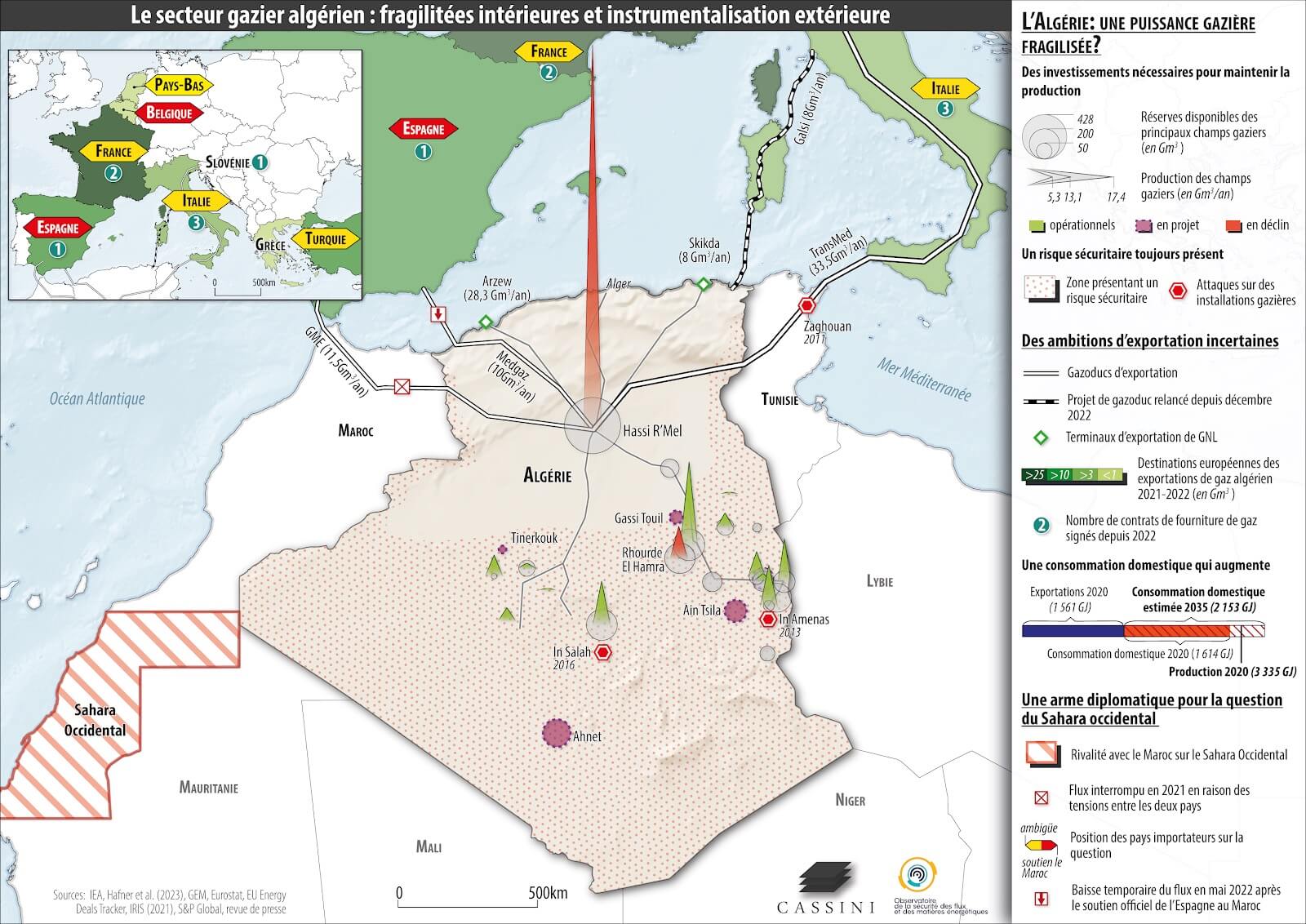
Cartographie géopolitique
Observatoire de la Sécurité des Flux et des Matières Premières Énergétiques (OSFME)
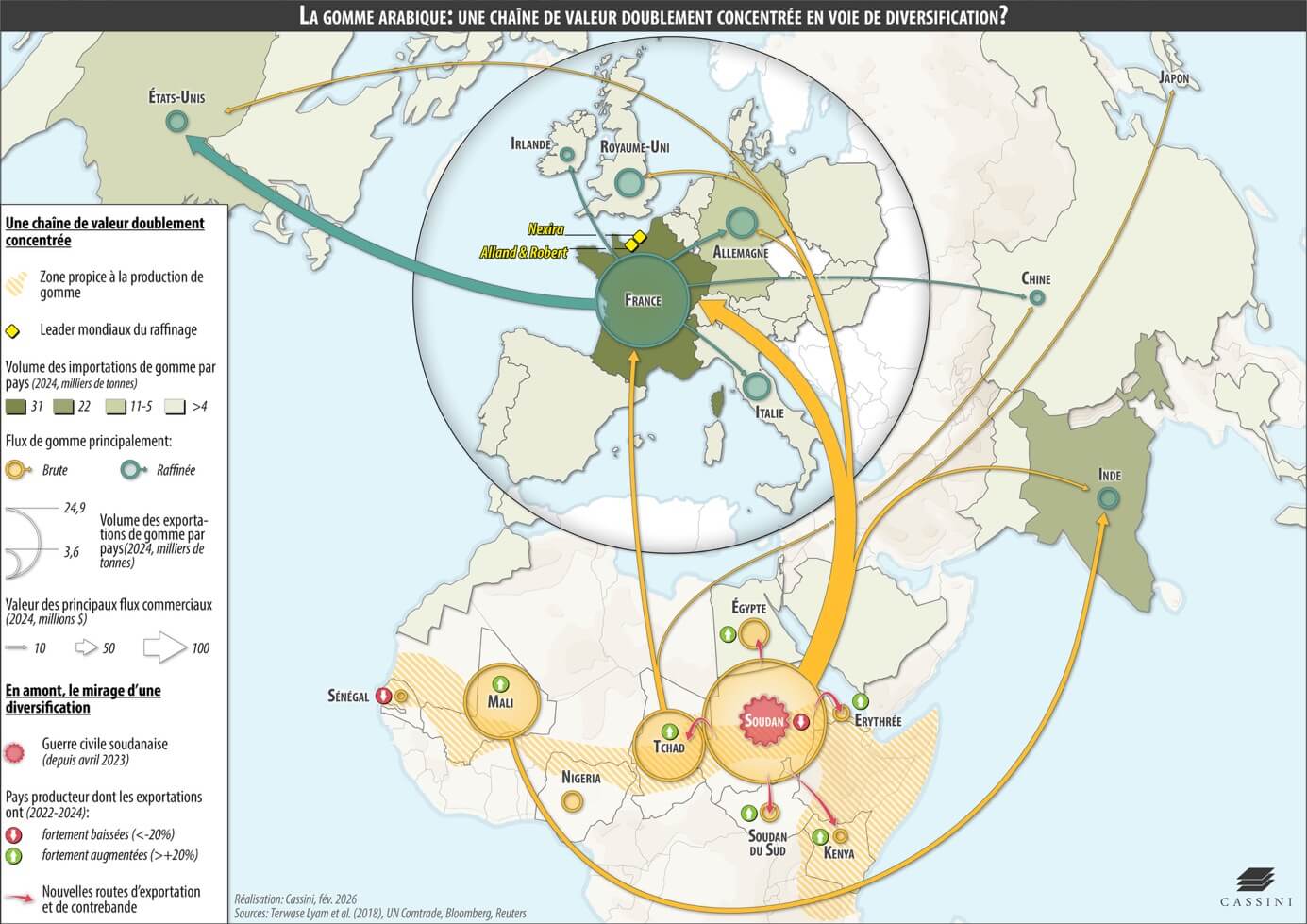
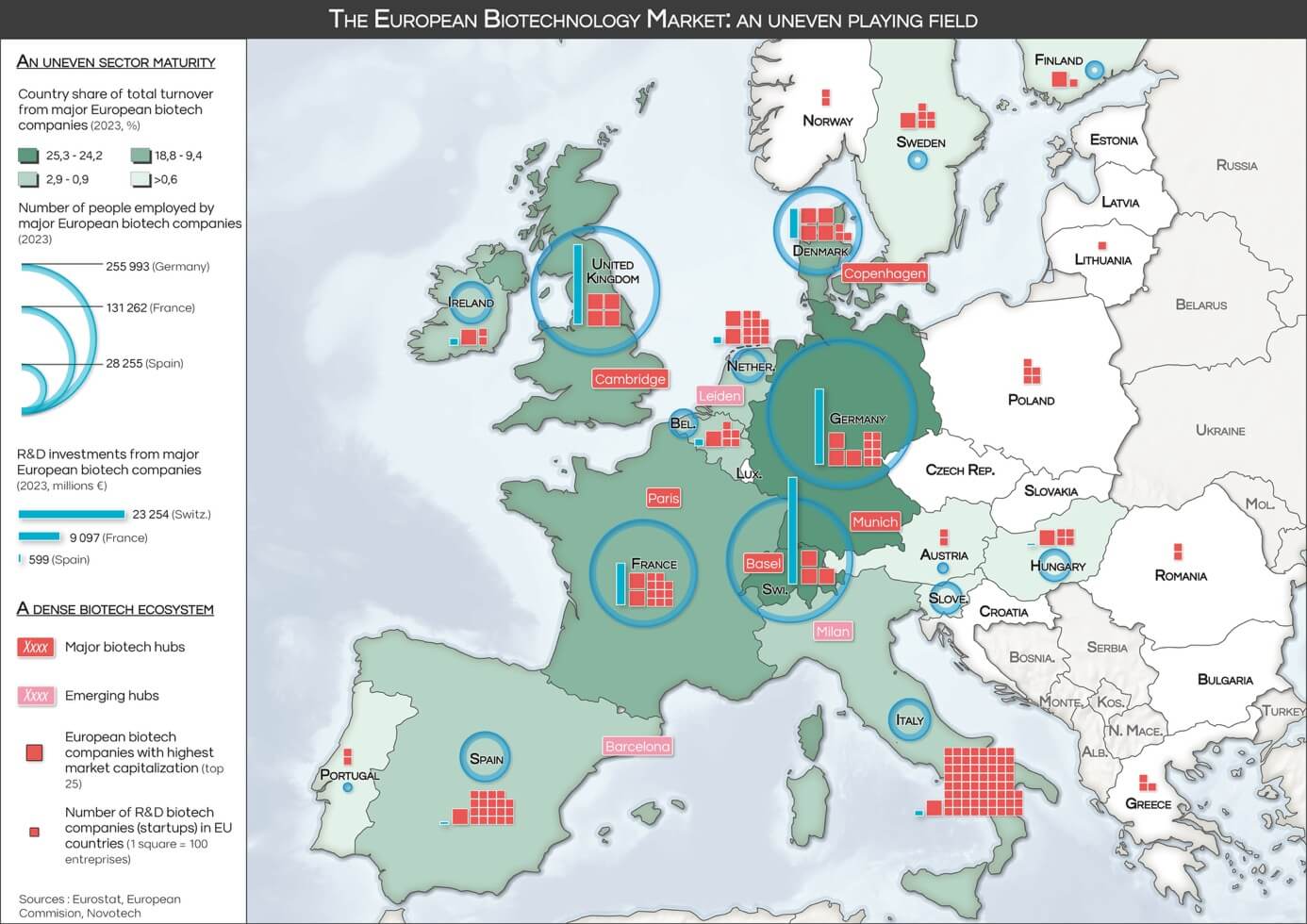
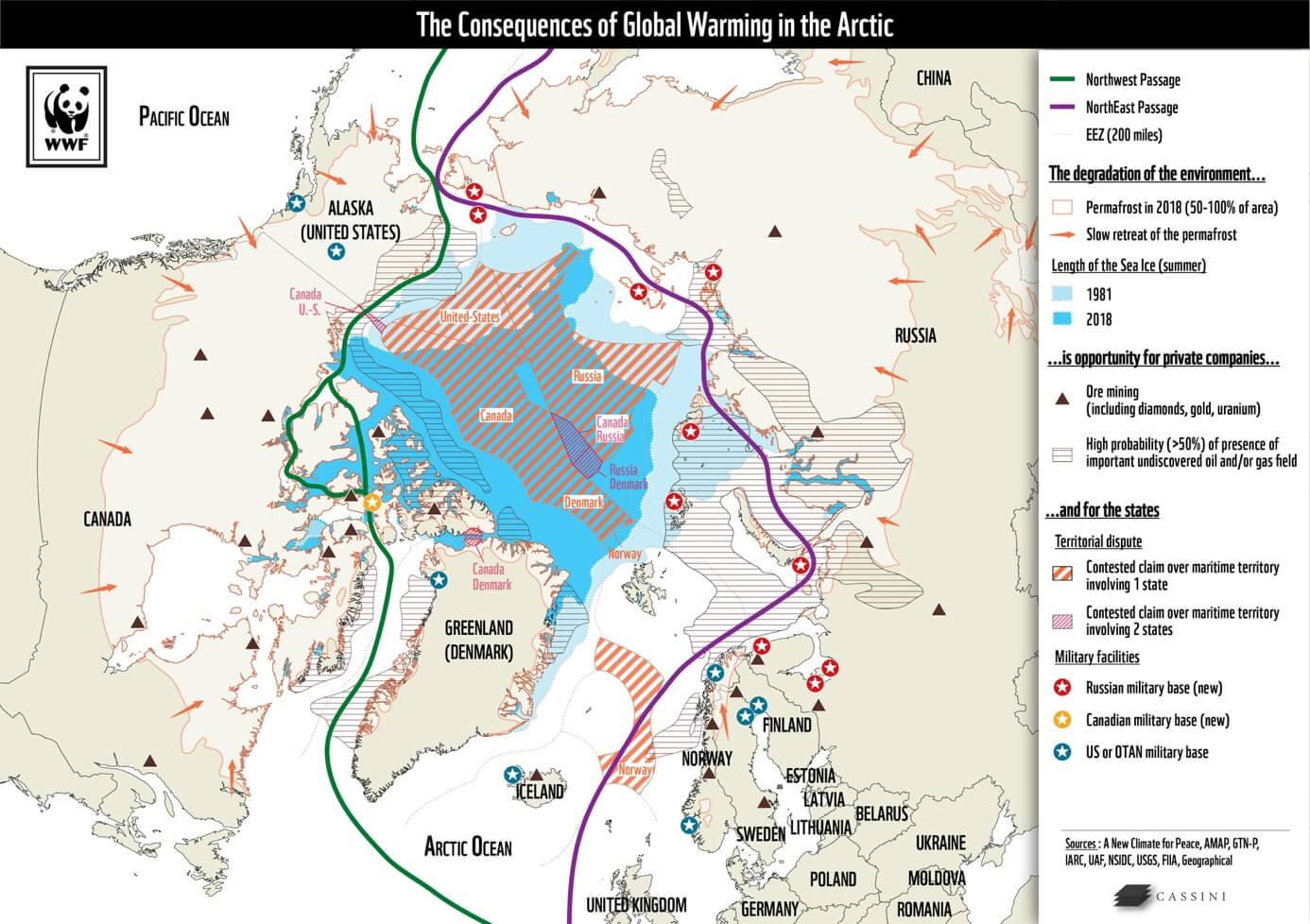
Depuis 2019, CASSINI contribue à l'Observatoire de la Sécurité des Flux et des Matières Premières Énergétiques (OSFME) pour le compte de la DGRIS du ministère des Armées, afin d'analyser les stratégies énergétiques des grandes puissances et de renforcer la capacité d'anticipation stratégique de la France.